Dave Tate
Category: Development
03.29.2018
Yesterday, on March 28, 2018, a major security update was released for the Drupal web content management system. Perhaps you have already seen intense headlines about Drupal security this week. Despite the severity of the vulnerability, on the whole, this is an example of security going well. I hope to clarify some misconceptions and provide a little more detail.
Drupal is Secured
First of all, the NJI Media team finished applying the patch to all our client’s websites within only a few hours of the release. The security of our client’s properties is our utmost concern and we were well prepared. Our engineers swiftly remediated the security issue across dozens of projects in short order, without any noticeable disruption to online services or production workflows. And we did it all without pizza, which apparently is non-standard practice.
Is Drupal secure? Yes, very. The Drupal Security Team credits the discovery of the vulnerability to Jasper Mattsson. Mattsson is a Drupal developer with Druid, a Drupal services firm specializing in security auditing.
At present, there is no known published PoC “proof-of-concept”. That is to say, the vulnerability is presently theoretical. As of writing, there is no known example of this issue compromising any site, nor any malicious script known to attempt to exploit the discovered vulnerability.*
The Response
The issue was reported to the Drupal Security Team (there is a Drupal Security Team). They promptly fixed it and released the fix. That is what created yesterday’s patch. To be clear, this is the order of events: Drupal developers proactively searched for theoretical problems, discovered one which appears to be unlikely to have been previously known or exploited, corrected it. Finally, they coordinated the release of the improvement for all users.
This is the first patch of this severity in about four years. It’s been dubbed Drupalgeddon (2, actually), but Drupal project owners need not be concerned if competent and security-conscious engineers maintain their project. If you’re an NJI Media client, you’re in the good hands of our outstanding team. (If you’re not with NJI Media, reach out now!)
The Drupal project has a stellar dedicated security team, and the announcement of this vulnerability is a testament to their diligence. As an agency maintaining many Drupal projects, we especially value their commitment to announce such security releases in advance. Suddenly releasing a patch without warning can lead to inadequate implementation, as teams may be ill-prepared to quickly provision adequate resources. The Drupal project appears to aim for Wednesday releases in general, and provides ample advance notice for major core patches. This decision makes it possible for agencies like NJI Media to ready a rapid response.
The Vulnerability
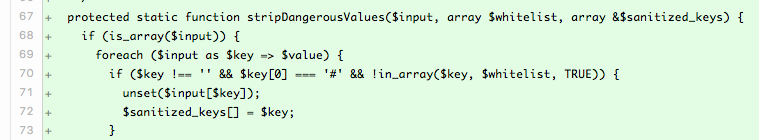
Having said all that, this was a serious vulnerability. The exploit would theoretically allow an attacker, without any authentication, to gain full control of the website. The patch is relatively simple, improving “sanitization” of visitor requests before the system further processes that data. Specifically, the vulnerability seems to lie in Drupal’s usual handling of input data keyed with the hash symbol. The patch strips away potentially malicious code from user data input from requests in URL query strings, form submissions, and cookies.
* Project maintainers absolutely must patch immediately. If they aren’t in the wild already, hacking and abuse of this issue is imminent. A catch in open source software security is that the publication of the fix is necessarily an advertisement of the problem. Would-be attackers probably weren’t aware of this vulnerability. They are now. This is why the issue was so well advertised — it’s not to scare users, it’s to make sure maintainers coordinate their response in a timely manner. Maintainers must patch immediately to defend against inevitable attempts to exploit this now-publicly-documented issue. It’s bad out there, but with vigilance and preparation, you can rest easy, and stay focused on your business objectives.